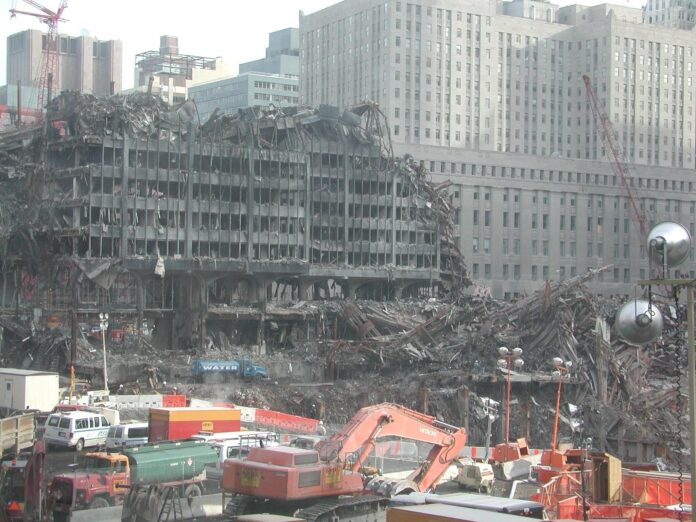
Nearly 18 years ago, we were blindsided when terrorists attacked the World Trade Center in New York City on Sept. 11, 2001. We now know that if there had been better information sharing between U.S. law enforcement and intelligence organizations that we may have been able to foil the plot. In the years since that devastating attack, the U.S. national security establishment has revamped its approach to information sharing for the purpose of counterterrorism. That new approach involves the systematic sharing of threat information across federal, state, local, tribal, territorial and international partners to ensure all have a picture of the threat and can react accordingly. These changes have improved our understanding of the terrorist threat and allowed for more proactive response when the threat manifests itself. Today, because of the whole-of-government approach to counterterrorism, we are better protected against physical terrorist attacks. But there is still a looming threat: cyber attacks on American critical infrastructure.
The cybersecurity community has yet to come together in a similar whole-of-government approach to address critical infrastructure cybersecurity. However, it is time to view cybersecurity and the protection of our cyber infrastructure through the same lens as we view protecting our country from terrorist attacks. In my view, our national approach to counterterrorism provides a great framework for our cybersecurity professionals to follow.
After the terrorist attacks of 9/11, the intelligence and law enforcement communities focused on connecting the dots, regardless of whether the information came from law enforcement, the intelligence community, the private sector, international partners or elsewhere. There was a concerted effort to increase information sharing among all stakeholders, and today there are strong mechanisms in place to share data seamlessly and globally around issues of security and terrorism.
This is not the case for our cyber infrastructure. Instead, there is fragmentation and distrust between the government and the owners and operators of the critical infrastructure in the U.S., 85 percent held by private companies. This fragmentation creates seams that foreign adversaries are able to exploit. It is time that we create a mechanism to foster greater information sharing across critical infrastructure sectors, the federal, state and local government and the private sector. Information needs to be more readily available on a “need to have” basis instead of just “need to know.” This effort will require more than just DHS and the new Cybersecurity and Infrastructure Security Agency (CISA) working closer with private industry. It will require buy-in and participation from across the federal government, international partners, private businesses, and state and local governments.
Currently, much of the information sharing process between government and industry is led through Information Sharing and Analysis Centers (ISACs). For example, the Oil and Natural Gas (ONG) ISAC has existed since 2014, and provides not just a trusted environment for information sharing but also security, ensuring that proprietary company information will not be compromised through the sharing of threat intelligence. The ONG and Downstream Natural Gas ISACs are the means by which the federal government works with private pipeline operators, many of which are members of one or the other ISAC, to provide two-way information sharing.
While the ISACs and other current information sharing networks are helpful, it’s not the whole-of-government approach that has been successfully fighting terrorism. It’s more than just DHS, FBI, and CIA that gather intelligence on cyber threats. The energy pipeline industry is a great example of the complexity of government organizations impacting industry cybersecurity, as there are at least four regulatory agencies providing intel and guidelines. There’s intelligence and information that comes from the everyday activities of the government, which should be more available to our private-sector partners as they work to protect their systems.
Making more information available to private-industry partners should be a priority for the government. However, information sharing is limited in part due to the lack of security clearances available to industry leaders. Beyond the well-known backlog of clearances and the hurdles individuals must surpass to gain a clearance, the process for private industry can be even greater. Given the propensity of over-classification of information across the intelligence community, this can prove to be a real barrier to our critical infrastructure leaders having the right kind of intelligence in a timely manner. The clearance process has discouraged some critical infrastructure owners and operators from participating in DHS’s information sharing and collaboration, according to the former head of US-CERT at DHS. Beyond improving the clearance process, the federal government can also be more judicious when classifying information on the front end.
If the country is serious about improving the cybersecurity of our critical infrastructure, then DHS would need to be given the authority to drive a whole-of-government approach to fusing intelligence from across the government and international partners, providing analysis, and increasing information sharing with industry partners. The National Counterterrorism Center is an example to follow, showing the effectiveness of a concerted effort to fight real threats. The threats we face today aren’t going to dissipate. It’s time for a new approach, where all parts of government that have equities in the cybersecurity of critical infrastructure come together to solve the problems.
The views expressed here are the writer’s and are not necessarily endorsed by Homeland Security Today, which welcomes a broad range of viewpoints in support of securing our homeland. To submit a piece for consideration, email [email protected]. Our editorial guidelines can be found here.