In early 2019, as Technology Co-Chair of the Federal IPv6 Task Force, I participated in intensive policy discussions with federal cybersecurity leadership about a critical national security imperative: transitioning federal networks to IPv6-only operations. The rationale was technically clear and strategically urgent. Operating dual-stack IPv4 and IPv6 networks doesn’t just add complexity, it fundamentally doubles the protocol attack surfaces. Every device running both protocols creates two parallel, protocol-specific vectors for exploitation, forcing defenders to secure and monitor twice the network-layer exposure. By contrast, single-stack IPv6 operations immediately halve the protocol attack surface, sharply reducing the federal government’s exposure to network-based cyber threats. This conclusion is not speculative; it is explicitly confirmed by RFC 7381, reinforced by peer-reviewed security research. Federal guidance, including CISA’s IPv6 Security Guidance and NIST’s Zero Trust publications, reinforce this analysis—dual-stack complexity directly increases attack surface exposure.
Every day spent dualstacked is a day spent with a doubled attack surface.
Federal cyber leadership has consistently emphasized enterprise defense, resilience, and modernization as top priorities. Those priorities cannot be fully realized while agencies remain dual‑stack, defending two protocols at once. Transitioning to single‑stack IPv6 is therefore not just a technical upgrade but a direct enabler of the resilience federal leaders have long demanded.
These discussions helped lay the groundwork for formal policy action the following year. In November 2020, the Office of Management and Budget issued Memorandum M-21-07, “Completing the Transition to Internet Protocol Version 6 (IPv6),” establishing that by fiscal year (FY) 2025, at least 80 percent of IP-enabled assets on federal networks must operate in IPv6-only environments. The memorandum was aligned with the framework we developed: firm deadlines, IPv6-only objectives, and cybersecurity-focused implementation.
That deadline — September 30, 2025 — has now passed. Yet, despite years of effort, many federal agencies remain noncompliant with the mandate. This is not a partisan issue. It is a technical and strategic imperative that transcends political considerations. The threat landscape does not pause for transitions of power. Attack surfaces do not shrink because of electoral outcomes. IPv6-only adoption is a national security necessity driven by mathematical realities, architectural requirements, and the demands of emerging technologies.
The question is no longer whether we will achieve it, but how much longer we are willing to tolerate the vulnerabilities that delay sustains.
“If Not Now, When?”—A Question Still Unanswered
In February 2020, I published “Adopting and Enforcing an IPv6-only Policy: If Not Now, When?” and urged that the federal government lead by example and set a firm deadline for implementing an IPv6-only policy – to demonstrate its commitment to securing cyberspace and protecting the nation’s critical infrastructure.
Five years later, that question remains incompletely answered. As of October 2025, no federal agency has publicly announced achieving the 80% IPv6-only compliance mandated by M-21-07. Given that such compliance would represent a significant achievement worthy of recognition, the absence of any such announcements strongly indicates that implementation has fallen well short of requirements. This conclusion is reinforced by federal IT community assessments, industry observations, and the documented technical and organizational challenges facing agencies—particularly the largest agencies with the most complex legacy infrastructure. We are not merely behind schedule; we are watching a critical national security initiative struggle to achieve traction despite clear policy direction and realistic timelines.
As someone who helped shape the policy framework and has publicly championed IPv6 only adoption for more than a decade, I share responsibility for these implementation challenges. Perhaps we underestimated organizational resistance to architectural change. Perhaps we overestimated agencies’ technical readiness. Perhaps we failed to adequately communicate the urgency beyond the cybersecurity community.
But the fundamental technical analysis was — and remains — correct. The implementation approach needs refinement, not the strategic objective.
The Technical Imperative: Why IPv6-only Matters
IPv6-only adoption is not a policy preference for debate; it is a technical necessity set by realities that transcend government administrations.
Address Exhaustion and Architectural Limitations
IPv4’s 4.3 billion addresses were exhausted more than a decade ago—top-level depletion in 2011 and North American depletion in 2015. Reliance on Network Address Translation (NAT) and other workarounds creates complexity, breaks end-to-end connectivity, and introduces security vulnerabilities. IPv6’s 340 undecillion addresses eliminate these constraints and enable architectures impossible in IPv4.
Attack Surface Reduction
The IPv4 and IPv6 dual stack mode of operation sustain vulnerability landscapes for both protocols. Adversaries exploit both IPv4 and IPv6 vulnerabilities, often leveraging transition mechanisms as additional vectors. Security researchers and federal guidance detail active exploitation during dual stack operations — every day spent dual stacked is a day spent with doubled attack surface.
Emerging Technology Requirements
IoT, industrial control, smart infrastructure, and most new emerging technologies depend on IPv6. IPv4’s address exhaustion makes it fundamentally unfit for mass-scale deployments. Agencies delaying IPv6-only adoption cannot effectively secure or manage expanding technology landscapes.
Zero Trust Architecture Dependencies
Zero Trust Architecture (ZTA) initiatives rely on explicit trust verification and microsegmentation. IPv6’s abundant address space enables granular controls, facilitating robust ZTA architectures more easily than IPv4’s constraints. Dualstack systems, by contrast, create management complexity and additional security risk, as controls and inspection must be configured and maintained for both protocols. This is fully documented in NIST SP 800207 (Zero Trust Architecture) and reinforced by the NSA/DoD IPv6 Security Guidance, which emphasize that IPv6-only environments simplify boundary filtering and strengthen ZTA implementation.
Strategic Positioning and Peer Adoption
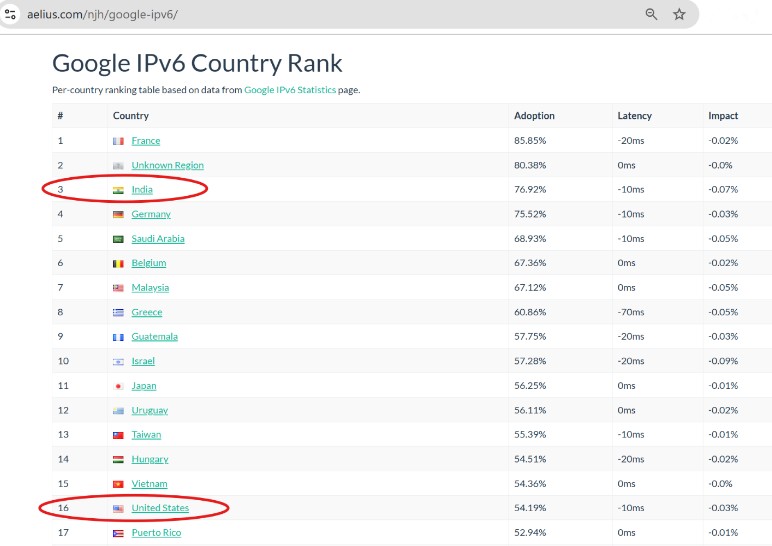
The United States has never been the global leader in IPv6 adoption. While federal mandates began as early as 2005, actual deployment lagged. Countries such as Belgium, India, France, and Germany surged ahead, with adoption rates exceeding 70–80 percent in recent years. By contrast, U.S. adoption hovers closer to 50 percent, ranking only around 17th worldwide as of March 2025 according to CircleID.
The disparity is clear in APNIC Labs IPv6 Measurement Data and corroborated by industry analyses CircleID and Cisco. Nations that embraced IPv6 early now operate closer to IPv6-only environments, reducing dualstack complexity and shrinking their attack surfaces. The United States, by remaining heavily dualstack, is most likely less secure than peers who have already consolidated on the single-stack of IPv6.
This is not just a matter of optics or international benchmarking. It is a matter of resilience. Countries with higher IPv6 penetration enjoy simplified architectures, lower operational costs, and stronger security postures. The U.S., by delaying, sustains the burden of dualstack operations — a burden adversaries can and do exploit.
While the United States lags, many other nations have advanced rapidly in IPv6 adoption. Belgium became the first country to surpass 50% capability in 2016, leading global adoption from 2014 through 2018. As of October 7, 2025, fifteen countries rank ahead of the U.S. in IPv6 adoption — including France, India, and Germany, each with adoption rates above 75%, according to public data. In recent years, India has accelerated its IPv6 deployment dramatically, pulling far ahead of the U.S. and many other nations.
According to APNIC Labs, as of October 2025 India’s IPv6 adoption rate exceeds 77%. This figure translates to more than 600 million active IPv6 users, placing India among the top two nations worldwide in IPv6 deployment. Independent confirmations drawing on APNIC’s measurement data reinforce this position. For example, Network World highlighted India’s rapid acceleration in IPv6 capability, noting that its scale and growth outpaced most of the Asia-Pacific region. Earlier in 2025, The Register reported India’s adoption at approximately 73–74%, confirming its leadership alongside France and other top tier nations.
As the accompanying chart shows, the U.S. stands only at number 16, trailing nations such as Vietnam. Unless this gap is closed, the United States risks ceding technological leadership in the very protocol that will define the next generation of Internet infrastructure.
These are material facts. The physics of networking and the mathematics of address space don’t change with political leadership. IPv6-only adoption is as inevitable as the historical transition from analog to digital communications. The question is whether we transition proactively and strategically, or reactively after security incidents force emergency change.
Why Implementation Has Lagged: An Honest Assessment
Understanding why federal agencies have struggled to meet the FY2025 deadline requires honest examination of technical, organizational, and cultural challenges—challenges I observed throughout my federal career and which I anticipated but perhaps underestimated.
Technical Debt and Legacy Systems
Federal IT infrastructure carries decades of accumulated technical debt. Systems built on IPv4 assumptions and applications with hard-coded IPv4 dependencies create additional challenges and make the IPv6-only transition take significantly longer, even if fundamental re-architecture isn’t strictly necessary.
Many agencies discovered their “IPv6-capable” systems were capable in name only—able to pass IPv6 traffic but with security tools, monitoring systems, and operational procedures that remained IPv4-centric. True IPv6-only operation required replacing or substantially upgrading core infrastructure at scale and cost beyond initial estimates.
Budget Constraints and Priority Competition
IPv6 transition competes against every other IT modernization priority in constrained budgets. Agencies prioritize immediate operational needs even when delayed transitions actually increase long-term risk — a choice that may seem practical in the short-term but is strategically misguided.
IPv6 Expertise Gap
The federal workforce, like the broader IT industry, lacks sufficient IPv6 expertise. Network engineers trained primarily on IPv4 face steep learning curves when adapting to IPv6’s distinct address structures, routing protocols, security models, and operational procedures.
Many agencies lacked the internal expertise to plan and execute large-scale transitions and struggled to find contractors with the necessary skills. In many cases, long-term contract staff assigned to agencies did not possess the required IPv6 capabilities, and even when contracts changed, much of the contractor workforce remained the same. As a result, technical debt has accumulated, and the shortage of qualified IPv6 skills needed to implement the transition remains severe.
This creates a vicious cycle: agencies delay IPv6 adoption because they lack expertise, which prevents them from developing expertise, which further delays adoption. Breaking this cycle requires dedicated training programs, knowledge transfer initiatives, and sustained commitment to workforce development.
Vendor Readiness Inconsistencies
While major network equipment vendors have supported IPv6 for years, the broader software ecosystem remains inconsistent and often lack true feature and performance parity. Critical applications, security tools, and operational management systems still have incomplete or inadequate IPv6 support. In many cases, agencies discovered vendor IPv6 implementations were incomplete (e.g., missing management hooks, differences in logging, limited feature support). Some vendors treated IPv6 as a checkbox feature rather than a fully equal protocol, creating situations where systems technically support IPv6 but with reduced functionality or performance.
Agencies remained constrained by vendor roadmaps, and vendor delays cascaded into agency delays. This is a market failure—insufficient customer demand for full IPv6 parity creates insufficient vendor incentive to invest in complete implementations.
Cultural Resistance and Risk Aversion
Perhaps most challenging is cultural resistance. IPv4 is known, understood, and comfortable. IPv6 is different, requires learning, and carries a perceived risk of disruption. In risk-averse government cultures, the tendency is to delay change until forced, particularly when existing systems appear to function adequately.
The irony is that maintaining IPv4 dual-stack operations carries far greater security risk than transitioning to IPv6-only. But that risk is familiar, normalized, and distributed across the entire federal government. The risk of transition—potential disruption, service interruptions, implementation challenges—is immediate, visible, and owned by individual agency leaders making decisions.
Accountability and Enforcement
Federal policy established requirements but provided limited accountability mechanisms for non-compliance. Without meaningful consequences for missing deadlines, agencies could deprioritize IPv6 transition in favor of initiatives with more immediate political or operational visibility. The mandate had ambition but lacked enforcement mechanisms.
Taken together, these six factors explain why the FY2025 mandate faltered. Technical debt and legacy systems slowed progress from the start. Budget pressures pushed IPv6 behind more immediate priorities. A persistent expertise gap left agencies unable to build confidence or momentum. Vendor inconsistencies compounded delays, while cultural resistance reinforced the instinct to postpone change. Finally, the absence of strong accountability mechanisms allowed deadlines to slip without consequence. The lesson is clear: success requires more than policy—it demands resources, skills, vendor alignment, cultural resolve, and enforceable accountability. Without addressing all six dimensions together, the cycle of delay will repeat.
The Security Cost of Delay
Every day spent dualstacked is a day spent with a doubled attack surface. While agencies grappled with implementation challenges, the threat environment did not pause. The security justification for IPv6-only adoption has only become more urgent.
Expanded Attack Surfaces
Every day federal networks operate in dual-stack mode, adversaries have twice the protocol landscape to exploit. Vulnerabilities in IPv4 implementations, IPv6 implementations, and the complex interaction between them create numerous attack vectors. Recent high-profile cyber incidents have demonstrated that sophisticated adversaries exploit complexity and inconsistency—precisely what dual-stack operations provide.
Adversary Capabilities Evolving
Potential adversaries have not stood still while we delayed. Their IPv6 capabilities, offensive cyber tools, and understanding of dual-stack vulnerabilities have evolved. Every month we delay IPv6-only adoption is a month adversaries gain relative advantage in understanding and exploiting the very transition mechanisms and dual-stack complexities we continue operating.
IoT and Critical Infrastructure Vulnerabilities
The explosive growth of Internet of Things devices, industrial control systems, and smart infrastructure creates expanding attack surfaces that IPv4 architectures cannot adequately secure. Federal agencies delaying IPv6 adoption find themselves unable to effectively manage these environments, creating critical infrastructure vulnerabilities with potential cascading consequences.
Zero Trust Implementation Gaps
Federal Zero Trust Architecture (ZTA) initiatives are undermined by continued IPv4 dependency. ZTA principles are more effectively implemented in IPv6 environments, and dualstack operations complicate implementation while reducing effectiveness. Agencies should develop their IPv6 and Zero Trust implementation plans simultaneously because the two work in tandem to improve network cybersecurity. With the proper IPv6 addressing architecture, it’s possible to have cleaner, less complicated boundary filters and more granular filtering for Zero Trust. Currently, dualstack systems create management complexity and additional security risk, as controls and inspection must be configured and maintained for both protocols, often reducing Zero Trust effectiveness. Every delay in IPv6-only adoption is a delay in achieving robust Zero Trust security, as full ZTA benefits require IPv6’s scale and segmentation.
Renewed Commitment to Execution
The Billington Cybersecurity Summit in Washington, D.C., in September 2025 provided a timely backdrop for reflection. With the September 2025 milestone now behind us, it was clear that the policy framework established in 2019 through OMB Memo M-21-07 remained sound: the analysis was correct, and the timelines were realistic. What has been lacking is not the framework, but the organizational will to execute it with urgency and accountability.
The mission is not finished. But it can succeed.
What Must Happen Next: A Path Forward
The path forward is not uncertain. The standards are written, the research is conclusive, and the policy framework is already in place. What remains is execution. Federal leaders must now move beyond dualstack hesitation and commit fully to singlestack IPv6. That means embedding milestones into agency performance plans, holding CIOs and CISOs accountable for delivery, and reporting progress transparently through public dashboards. The technical case is settled; the strategic imperative is undeniable. The only question left is whether we will summon the will to finish the mission. The time to act is now.
That urgency is sharpened by the fact that the September 30, 2025 deadline has passed, but the mission has not failed. It has simply entered a new phase — one that demands renewed commitment, stronger accountability, and decisive strategic intervention. What follows are specific, actionable recommendations drawn from my three decades of experience across both the public and private sectors, including leadership roles delivering state-of-the-art technical solutions nationwide. They reflect a deep, hard-earned understanding of what succeeds — and what does not — in large-scale federal technology transformation. These recommendations are offered as my personal perspective, grounded in professional practice and informed by lived experience.
To finish the mission, federal leaders must act on seven priorities: conduct immediate, transparent assessments of IPv6-only status; establish binding interim milestones through 2028; create a CISAled IPv6 Center of Excellence; enforce accountability through budgets, reporting, and leadership evaluations; close vendor gaps with full IPv6 procurement requirements; invest in workforce development to build lasting expertise; and integrate IPv6-only adoption into Zero Trust, cloud migration, modernization, and cybersecurity strategies. Together, these steps transform IPv6-only from a deferred mandate into the foundation of federal digital resilience.
Phase One: Establish the Ground Truth and Reset the Clock
- Conduct Immediate Assessment and Transparency
- Every agency must report detailed IPv6-only implementation status by December 31, 2025 (or within 90 days of normal operations resuming if disruptions persist).
- Reports must go beyond percentages: specify which systems are IPv6-only, which remain dualstack, and what barriers block transition.
- Transparency creates accountability; public reporting creates pressure; detailed assessment enables targeted assistance.
This assessment is not about producing another compliance snapshot; it is about exposing the operational reality of federal networks. By requiring agencies to identify which systems remain dualstack and why, leaders can separate technical debt from vendor dependency and cultural resistance. That clarity allows policymakers to target interventions precisely — whether through funding, vendor mandates, or leadership accountability — and ensures that the path forward is based on facts, not assumptions.
Without transparency, there can be no accountability — and without accountability, there will be no progress.
- Establish New Interim Milestones
- Agencies that missed FY2025 must adopt binding targets:
- 60% IPv6-only by September 30, 2026
- 80% IPv6-only by September 30, 2027
- 100% IPv6-only by September 30, 2028
- Embed these milestones in performance plans with CIO/CISO accountability.
- Require quarterly reporting with public dashboards tracking agency status.
Milestones are not arbitrary dates; they are instruments of discipline. Phased targets allow agencies to pace their transitions, measure progress, and avoid the “big bang” failures that come from deferring action until the final deadline. These checkpoints also give OMB and CISA the visibility to identify laggards early and intervene before failure becomes systemic.
Crucially, these milestones are achievable — but only with the comprehensive support infrastructure that was absent from the original M-21-07 implementation. A dedicated IPv6 Center of Excellence, robust training programs, coordinated vendor engagement, and clear accountability mechanisms will provide the scaffolding agencies need to succeed.
Deadlines matter because they drive discipline, and discipline is the difference between aspiration and achievement. Yet deadlines alone are not enough. To make these milestones real, agencies must be equipped with the tools, support, and accountability structures that will carry them across the finish line.
The following five priorities provide that foundation.
Deadlines drive discipline — and discipline is the difference between aspiration and achievement.
Phase Two: Deliver the Infrastructure to Succeed
- Create an IPv6 Center of Excellence (CISAled)
- Technical Assistance: architecture reviews, security assessments, troubleshooting.
- Reference Architectures: deployment templates, configuration guides, security frameworks.
- Training Programs: comprehensive IPv6 training and certification for federal IT staff.
- Vendor Coordination: centralized engagement to close product gaps and align roadmaps.
- Knowledge Sharing: forums, case studies, and collaboration platforms.
Agencies should not be left to reinvent the wheel. A centralized Center of Excellence ensures that lessons learned in one agency become shared assets for all. By consolidating expertise, standardizing architectures, and coordinating vendor engagement, the federal government can accelerate adoption while reducing cost and risk. This model has worked in other domains — cybersecurity, cloud, and Zero Trust — and it must now be applied to IPv6.
A Center of Excellence transforms isolated struggles into shared success.
- Implement Accountability Mechanisms
- Budget Leverage: prioritize IT modernization funding for agencies showing IPv6-only progress.
- Elevated Reporting: require noncompliant agencies to submit monthly remediation reports to OMB and CISA.
- Mandatory Assistance: agencies far behind must use the IPv6 Center of Excellence.
- Leadership Accountability: CIO/CISO evaluations must explicitly include IPv6-only progress.
Accountability is the missing ingredient in federal technology transformation. Without consequences, deadlines slip and priorities fade. By tying funding, reporting, and leadership evaluations directly to IPv6-only progress, the government can ensure that this mandate is treated not as optional guidance but as a binding requirement.
Accountability is not punishment — it is the engine of progress.
- Address Vendor Gaps Systematically
- Federal procurement must require full IPv6 parity, not minimal “IPv6capable” compliance.
- Contracts should include IPv6 requirements, testing protocols, and remediation clauses.
- Federal purchasing power should drive market transformation by making IPv6 parity nonnegotiable.
Vendors respond to market signals, and the federal government is the largest IT customer in the world. By demanding full IPv6 parity in every contract, the government can close product gaps, accelerate vendor roadmaps, and ensure that agencies are not forced to maintain insecure dualstack environments. Procurement is policy — and in this case, it is the lever that can reshape the entire marketplace.
When the federal government demands parity, the market delivers it.
- Invest in Workforce Development
- Establish IPv6 training requirements for all network and security staff.
- Create career pathways recognizing IPv6 expertise.
- Partner with universities and training organizations to expand the curriculum.
- Incentivize certification and advanced skill development.
- Build internal IPv6 expertise to reduce contractor dependence.
Technology transitions succeed or fail on the strength of the workforce. IPv6-only adoption requires not just technical skill but cultural confidence — the assurance that federal staff can design, operate, and secure these networks without perpetual reliance on contractors. By investing in training, certification, and career pathways, the government builds enduring capacity that will sustain modernization long after the initial transition is complete.
Technology endures only when people are trained to sustain it.
- Integrate IPv6-only with Broader Federal Initiatives
- Zero Trust Architecture: make IPv6-only a prerequisite or parallel requirement.
- Cloud Migration: require IPv6-only by default.
- IT Modernization: embed IPv6-only requirements into all projects.
- Cybersecurity: frame IPv6-only as foundational architecture, not an optional upgrade.
IPv6-only cannot be treated as a siloed initiative. It is the connective tissue that enables Zero Trust, cloud adoption, and modern cybersecurity. By embedding IPv6-only requirements into every modernization effort, the government ensures that resources are aligned, duplication is avoided, and security is strengthened at the architectural level.
IPv6-only is not a side project — it is the backbone of federal modernization.
Taken together, these seven priorities form more than a checklist — they are a blueprint for finishing the mission. Transparency exposes the truth, milestones enforce discipline, a Center of Excellence spreads expertise, accountability ensures follow-through, procurement reshapes the market, workforce development builds lasting capacity, and integration embeds IPv6-only into the very fabric of federal modernization. This is not theory; it is a practical, achievable path forged from three decades of lessons learned. The question is no longer whether IPv6-only is necessary, but whether we will summon the will to execute. The time for hesitation has passed.
The time for leadership is now.
A Personal Reflection: Three Decades, One Mission
I have spent more than three decades in IT across both the public and private sectors, including sixteen years in federal leadership roles spanning multiple agencies. I have designed networks, built data centers, led engineering teams, overseen large-scale infrastructure deployments and upgrades, and shaped policy at the highest levels. Through it all, one technical truth has become undeniable: IPv6-only adoption is not optional. It is inevitable.
For more than a decade, I have championed this transition — not because it is easy or convenient, but because it is essential to the future of cybersecurity. I have written articles, spoken at conferences, briefed senior leaders, consulted with Internet pioneer Dr. Vint Cerf (co-creator of TCP/IP) on IPv6 policy and implementation challenges, engaged CEOs, CIOs, and CISOs, contributed to policy development, and advocated relentlessly for what the technical evidence makes clear must be done.
As Technology Co-Chair of the Federal IPv6 Task Force, I led monthly Technical Roundtables and shaped implementation strategy across federal agencies. In 2015, my Task Force co-chair, Rene Smeraglia, publicly recognized me as an IPv6 thought leader within the U.S. government, reflecting early acknowledgment of my sustained advocacy and technical leadership. Over the years, that reputation has grown across the federal IT community, where colleagues and conference peers have come to identify me as the government’s principal IPv6 advocate — a reflection of both technical mastery and enduring commitment to advancing IPv6-only adoption.
Today, through Alliance for Universal Computing™, I continue this work from a new platform, carrying forward the same conviction: the mission is unfinished, and its success is still within reach. My commitment to IPv6-only adoption is not tied to any government position, political administration, or organizational affiliation. It is rooted in technical truth and strategic necessity that transcend these temporary structures.
I am sometimes asked whether I am frustrated by the pace of progress. The honest answer is yes — but also no.
Yes, because I know we could have achieved this by now. The technical path is clear. The policy framework is sound. The timelines were realistic. With sufficient commitment and prioritization, federal agencies could be operating primarily IPv6-only today, with dramatically reduced attack surfaces and fundamentally stronger security postures.
But also no, because I understand that important transformations take time. Changing entrenched architectures, overcoming cultural resistance, developing expertise, and achieving organizational alignment across the vast federal enterprise is inherently difficult. Progress often comes more slowly than advocates hope but faster than skeptics predict.
What matters is sustained commitment to the correct long-term objective, even when short-term progress is disappointing.
Three decades in, I remain as committed as ever — not to a job title or agency, but to a technical truth and a strategic imperative. IPv6-only adoption is not just a protocol shift; it is a security foundation, a future-proofing strategy, and a moral obligation for those entrusted with digital stewardship. The mission continues, and so do I.
Why History Will Prove This Vision Correct
In a decade, when IPv6-only operations are standard practice, history will look back on the 2020s and ask why it took so long to embrace the inevitable. The mathematics of address space do not change. The security imperatives do not change. What must change is organizational will.
Every major transition in the history of computing—analog to digital, on-premises to cloud, static to software-defined—was resisted before it was accepted. IPv6-only adoption is no different. It represents not merely a protocol change but a paradigm shift in how nations build and defend digital infrastructure. When that shift is complete, it will be remembered not as a technical footnote, but as a defining milestone in the modernization of global networks and the strengthening of national resilience.
Technical realities always prevail over inertia. The only question has ever been when.
Moving Forward: Alliance for Universal Computing
Through the Alliance for Universal Computing™ (AUC), I continue this mission on a global scale—building upon the foundation established through the federal IPv6 transition to advance a broader vision: a universally interoperable, sustainable, and secure computing ecosystem.
AUC’s purpose extends beyond IPv6-only adoption. It seeks to unify global efforts around open, standards-based architectures that promote secure, future-ready digital infrastructure. By convening public and private organizations, academic institutions, and technical communities worldwide, AUC aims to accelerate innovation, strengthen cybersecurity by design, and advance sustainability and resilience as core principles of digital transformation.
The work continues. The mission endures. The vision remains clear: to build a connected world where universal computing standards enable both progress and protection for generations to come.
Conclusion: The Question Endures
Five years ago, I asked: “If not now, when?” The deadline has passed. The urgency has only intensified.
Federal IPv6-only adoption is a national security imperative — rooted in technical reality and driven by global competition. The policy is in place. The framework is sound. The leadership exists. What remains is execution.
- To federal IT leaders: The mission is clear. Execute with urgency.
- To policymakers: Sustain accountability, resources, and focus.
- To the cybersecurity community: Advocate relentlessly and support agencies in transition.
- To the American people: Demand secure digital infrastructure from your government.
Every day of delay expands the attack surface. Every hesitation deepens strategic disadvantage. Let us answer “If not now, when?” decisively — with intentional, urgent, and strategic execution.
The transition to IPv6-only is inevitable. Let us make it intentional, successful, and secure — for the nation and its future. IPv6-only is not a future option. It is the present mandate. History will measure us by whether we had the will to finish the mission.
Disclaimer: This article represents the author’s professional analysis and perspective based on nearly two decades of federal IT leadership and IPv6 policy development. The views expressed are those of the author.